Product Function
-

Coverage Area
The geolocation covers 4.3 billion IP, including all network equipment, such as PC, mobile phone, etc.
-

Geolocation Precision
Range of ultra-high precision geolocation can reach 50m to 5km, county-level geolocate to county center.
-

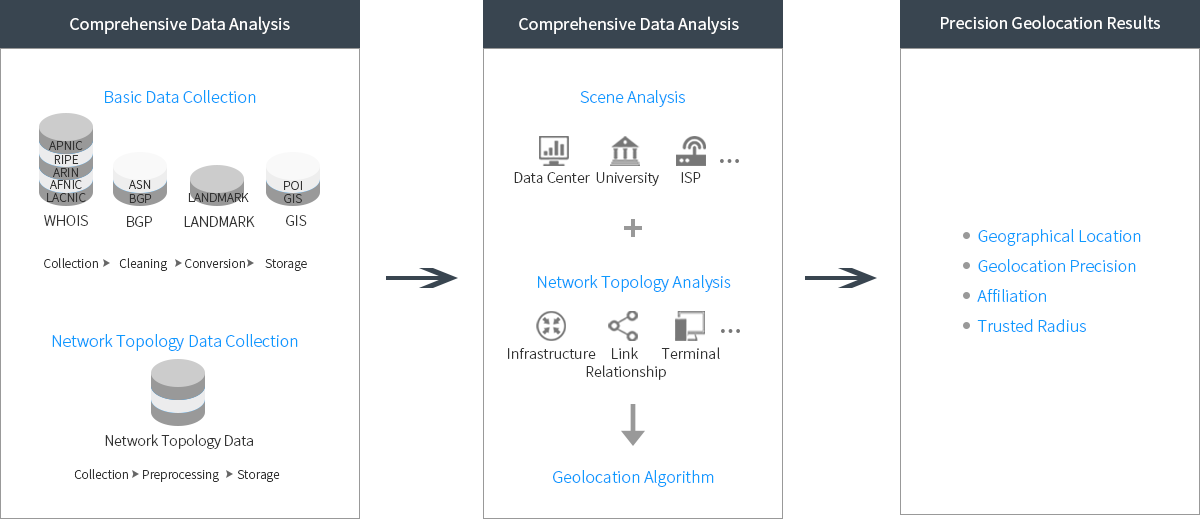
Geolocation Results
Geolocation result returns continent, country, province, city, county, longitude and latitude, zip code, operator and other information.
-

Update Frequency
Ultra-high precision API, weekly update;district level API, daily update.
-

Product Performance
It supports 1000 times/second concurrency, and returns the geolocation result in 10 ms.